AppManager 6.0.2 Trial
By: SUSE View more from SUSE >>
Download this next:
12 top enterprise risk management trends in 2023
By: TechTarget ComputerWeekly.com
Type: eGuide
Enterprise risk management has taken center stage as organizations grapple with the lingering effects of the COVID-19 pandemic, the threat of a recession and the rapid pace of change.
Executives recognize that stronger ERM programs are required to remain competitive in this new era. One aspect of the current risk landscape that companies must contend with is the connectivity of risks.
Businesses are increasingly more interconnected to partners, vendors and suppliers across global markets. As a result, the impact, for example, of a local natural disaster, the ongoing war in the Ukraine or high interest rates can cascade across an entire global supply chain.
Here are 12 security and risk management trends that are reshaping the risk landscape and influencing business continuity planning.
These are also closely related to: "AppManager 6.0.2 Trial"
-
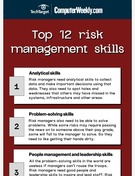
Infographic: Top 12 risk management skills
By: TechTarget ComputerWeekly.com
Type: Infographic
Risk management is a must for anyone who aspires to be a leader or manager. There is risk to be addressed at all business levels, and if a leader is unable to manage risk, their upward mobility will disappear.
Being a capable risk manager requires awareness and knowledge to uncover potential risks and present them to people best suited to solve the problem. A risk manager doesn't necessarily have to make the fix -- they just need to bring it to the person who can.
-
Focus: how to avoid being hit by ransomware
By: TechTarget ComputerWeekly.com
Type: eGuide
The global ransomware attack of May 2017 that affected more than 200,000 computers in over 150 countries shocked many business and political leaders – not least in the UK, where parts of the National Health Service were forced to restrict operations and turn away patients.
But the scale of the attack came as less of a surprise to IT and information security experts, who have been predicting an incident of this severity for a long time.
Will the rapid spread of the WannaCry exploit finally be a wake-up call to organisations to take cyber security more seriously? Only time will tell – but there are no more excuses for not being prepared for further ransomware threats.
In this special report, we analyse the risks of ransomware and provide the latest best practice advice on how to protect your organisation from this fast-growing form of malicious software.
Find more content like what you just read:
-
A Computer Weekly buyer's guide to managing paper processes
By: TechTarget ComputerWeekly.com
Type: eGuide
Modern paper processes are ripping up the rule book. In this 13-page buyer's guide, Computer Weekly looks at risk mitigation, security measures for connected printers and the shift towards end-to-end digitisation.
-
Infographic: 5 questions to ask when creating a ransomware recovery plan
By: TechTarget ComputerWeekly.com
Type: Infographic
Companies need extensive plans to successfully protect themselves from ransomware attacks. These 'five W's of ransomware' will help organizations ask the right questions when creating a ransomware-specific disaster recovery plan.
-
Today's attacks target people, not just technology
By: Proofpoint
Type: White Paper
Today's threat landscape requires a fresh mindset and new strategy, one that focuses on protecting people. In this white paper, explore the factors that play into end-user risk and how to mitigate these factors. Also, find concrete steps that your organization can take to build a people-centric defense.
-
Global Risks Report 2017
By: TechTarget ComputerWeekly.com
Type: Essential Guide
Society is not keeping pace with technological change, with artificial intelligence and robotics offering the greatest benefits but also the greatest negative effects, this report from the World Economic Forum reveals
-
Royal Holloway: Lessons on catastrophe - differences and similarities between cyber and other forms of risk
By: TechTarget ComputerWeekly.com
Type: Resource
Cyber insurance is still in its infancy but has shown significant growth, with evidence for further expansion. However, a lack of past information and some idiosyncrasies make pricing difficult, as well as potentially amplifying risk exposure. This article summarises findings from a practical model that could be used in lieu of actuarial data.
-
MicroScope - July-August 2024: Is it worth taking a risk?
By: MicroScope
Type: Ezine
In this issue, we take a closer look at the channel's approach to risk, with experts weighing in on with their approach to playing it safe versus taking steps towards innovation. Also read up on why the time is now to learn about AI-capable PCuse cases, as well as why the human factor should not be underestimated when it comes to AI
-
Anticipate, prevent, and minimize the impact of business disruptions
By: ServiceNow
Type: Buyer's Guide
Read this guide to discover how you can enable confident risk-based decisions across business and IT by building a proactive, comprehensive and competitive resilience strategy—especially in times of uncertainty and disruption.
-
Threat management: Essential guide
By: TechTarget ComputerWeekly.com
Type: eGuide
Security is about reducing risk, while assessing risk is all about understanding the cyber threats facing the enterprise, which in turn is about recognising that not all threats are external and that threat intelligence is a key element of threat management.
-
Step-by-step disaster recovery planning guide
By: TechTarget ComputerWeekly.com
Type: eBook
IT disaster recovery is a fundamental task for all organisations. Reasons range from legal and regulatory compliance to the ability to function after an outage. In this e-guide we outline in detail the key steps of disaster recovery planning.
-
Oracle cloud applications exhibit pragmatic adoption curve
By: TechTarget ComputerWeekly.com
Type: eGuide
Oracle prides itself on the full suite of the business applications it offers in the cloud, arguably ahead of its closest rival, SAP – which has prioritised building on its in-memory database Hana over the cloud per se, though its S/4 Hana ERP system is increasingly delivered over the cloud, too.
-
Managing risk in the age of data privacy regulation
By: Tanium
Type: White Paper
If your business is a victim of a data breach, you’ll possibly face not only financial and reputational damage but also legal repercussions. And as more data privacy regulations emerge, it becomes even more challenging for your organization to ensure across-the-board compliance. Inside this white paper, discover tips for managing regulatory risk.
-
Royal Holloway: Driverless vehicle security for military applications
By: TechTarget ComputerWeekly.com
Type: Research Content
Existing attacks and risk assessment frameworks within civilian autonomous vehicles (AVs) can be used to review security of military AVs deployed for logistics purposes in a desert warzone environment.
-
CW Innovation Awards: Sime Darby ups ante in service management
By: TechTarget ComputerWeekly.com
Type: eGuide
In this case study, learn how Sime Darby Industrial's inService Suite has returned more than 100,000 hours to the company in a digitisation initiative that has improved efficiency and customer engagement.
-
Object Storage 101
By: TechTarget ComputerWeekly.com
Type: Essential Guide
Standard file and block storage have their places, but there is an increasing move to object storage to meet the governance, risk and compliance needs of organisations, while also providing enhanced information management capabilities, say analysts Clive Longbottom and Marcus Austin.
-
Views from the c-suite: why endpoint management is more critical than ever before
By: Tanium
Type: White Paper
What were once your successful defense strategies have been outpaced by advancements in cyberthreats, leaving your endpoints vulnerable to attacks. So, how can you strengthen your endpoint security? By setting in motion 10 strategies for endpoint management. Dig into this white paper to unlock them.
-
Secure AI Coding Tool Adoption Challenges and Opportunities
By: AWS Snyk
Type: Research Content
This study assesses organizational readiness and concerns about adopting generative AI coding tools. Many are ready, but security worries persist as a key obstacle. Steps like POCs and developer training are often missed. Read the full report for insights on role-based perspectives and secure AI tool adoption strategies.
-
To hack back or not to hack back ...
By: Hewlett Packard Enterprise
Type: eGuide
This e-guide discusses hacking back as a viable option to combat hacking attempts. Expert Kevin Beaver discusses the merits and drawbacks of an "offense is the best defense" approach to security and how to implement more permanent security tools moving forward.
-
UC suite guide: Understanding what your organization needs
By: Intermedia
Type: White Paper
Today, organizations need effective collaboration and communications systems that can help them connect wherever they are. However, with so many unified communications solutions on the market, how can you know which one is best for your needs? Access this white paper to learn more.
-
Microsoft Azure AI Services on Dell APEX Cloud Platform
By: Dell Technologies
Type: White Paper
Read this paper to learn how pairing Azure AI services with Dell APEX Cloud Platform for Microsoft Azure, organizations can leverage the value of Azure AI's suite on-premises with APEX Cloud Platform.
-
How to choose HR software
By: Microsoft
Type: White Paper
Evaluating HR software can be complex. Our new, free 40-page guide to choosing HR software is a great place to start. It's yours now in exchange for taking our short survey on your employee experience purchase plans.
-
CW Brasil - Março 2022: Tolerância zero para conformidade de segurança corporativa
By: TechTarget ComputerWeekly.com
Type: Ezine
Como o modelo de confiança zero ajuda a reduzir as lacunas de segurança e cumprir os requisitos de governança nas empresas?
-
A Computer Weekly eGuide to Workspaces
By: TechTarget ComputerWeekly.com
Type: eGuide
In this eGuide we focus on all thing's workspace related. We dive into Google's new privacy settings, how the landscape of workspaces will look when the world of work fully returns and Google's new G Suite workspace overhaul.
-
15-minute interview: What is SAP S/4HANA and how do I migrate?
By: TierPoint
Type: Resource
An ERP system can make or break a business. The latest iteration of the SAP ERP can revolutionize business processes with intelligent automation. It’s called SAP S/4HANA, short for SAP Business Suite 4 running on HANA. This interview explores the opportunities and challenges of SAP S/4HANA migration. Read and watch the full interview here.
-
Cloud migration in 2024: Azure & Zones
By: Zones, Inc.
Type: eBook
This eBook discusses the benefits of migrating to the cloud & leveraging Azure services. It explores how Azure enables scalability, enhances security & productivity. Read the full eBook to learn how to upgrade your business.
-
All-In-One Videobars Aren’t All-Purpose Solutions – What IT Providers Need to Know
By: Shure Inc
Type: Blog
Despite the potential convenience of all-in-one video conferencing and collaboration systems, many of these technologies aren’t all-purpose solutions and can leave a lot to be desired when it comes to user experience. Browse this article to learn more.
-
5G vs. Wi-Fi 6: What's the difference?
By: TechTarget ComputerWeekly.com
Type: Infographic
Remote access to corporate resources is essential to ensuring business continuity, and there are a variety of ways to provide this access. VPN and DaaS can both give remote users access to an organization's resources, but they differ in key ways such as user-friendliness, performance, security and manageability.
-
Public vs. private vs. hybrid cloud S/4HANA and ERP deployments
By: Microsoft, Intel, SAP
Type: White Paper
In this expert e-guide, we explore how to future-proof your ERP system and increase its flexibility. Learn about the migration to S/4HANA as well as the pros and cons of private vs. public vs. hybrid cloud-based ERP deployments.
-
A Computer Weekly E-guide to NAS
By: TechTarget ComputerWeekly.com
Type: eGuide
In the guide we look at the fundamentals of NAS and the use cases it best suits, the range of file access storage products available including in the cloud and in hybrid operation between cloud and datacentre. We also examine the question of NAS backup, looking at the challenges that have accompanied it and the solutions available.
-
Build secure, threat-resistant apps
By: StarHub
Type: Product Overview
In today's digital landscape, mobile applications have emerged as a valuable tool for boosting productivity, but they also bring considerable risks. In this white paper, discover how StarHub Mobile Application Protection Suite (MAPS) empowers enterprises to build secure and robust mobile apps that can withstand attacks.
-
CW ANZ Jan 2019: Keeping pace with microservices
By: TechTarget ComputerWeekly.com
Type: Ezine
In this edition of CW ANZ, we look at how enterprises are using microservices to solve problems and the challenges they are facing in moving to this new paradigm in software development. Read the issue now.
-
Recent BI and Reporting Trends for Oracle EBS
By: Noetix Corporation
Type: eBook
Are you able to effectively leverage and report on Oracle eBusiness Suite data? Read this expert e-book to find out the latest technology trends that may affect your BI and reporting strategy. Learn more about how to get the most out of included BI/reporting features, when to use OBIEE and when you may need to consider alternative tools.
-
Top IT security priorities: Addressing risk management and compliance
By: Dell Software
Type: eGuide
In this expert e-guide, we explore the issues of IT risk management and compliance. You'll learn about best practices for audits, the role log reviews play in monitoring IT security, how to build authentication into access management systems, and more.
-
Endpoint and antimalware protection for small to large businesses
By: Carbon Black
Type: eGuide
Picking a security platform can be difficult. Inside this e-guide, expert Ed Tittel explores strategies and criteria to ensure you are picking the most successful security platform for your company.
-
Computer Weekly - 17 August 2021: How to choose between SIEM and SOAR
By: TechTarget ComputerWeekly.com
Type: Ezine
In this week's Computer Weekly, our buyer's guide examines the use of SIEM and SOAR to improve IT security, and asks which you should use, and when? We look at what you need to know about NVMe over Fabrics, the emerging storage networking technology. And we find out how Oracle customers are introducing its Fusion Cloud suite. Read the issue now.
-
Disaster recovery and business continuity: Essential guide
By: TechTarget ComputerWeekly.com
Type: eGuide
Not only can a solid business continuity strategy protect organisations from reputational damage and lost trade, but – for those operating in regulated industries – it can also prevent firms being hit with downtime-related enforcement action.
-
Top 6 Questions Answered About Transitioning to S/4HANA
By: TierPoint
Type: Analyst Report
Explore the top 6 questions answered by Gartner about transitioning to S/4HANA in this report.
-
Cybersecurity solutions built for today’s cloud-centricity
By: Palo Alto Networks
Type: Product Overview
According to Gartner, by 2025, 95% of new digital workloads will be on cloud-native platforms. With organization’s moving rapidly to the cloud there is a fresh demand for modern cybersecurity. Read this product overview to learn about Palo Alto’s Cloud Next Generation Firewall (NGFW), an offering designed to meet today’s cloud-centric demands.
-
Key data governance considerations: Picking the right tool for you
By: Veritas
Type: eGuide
In this expert e-guide, we explore key evaluation factors for selecting the right data governance tool to suit the needs of your organization. Find out which metrics matter most when it comes to picking your tool, like handling metadata objects, managing data quality, addressing unstructured data, and more.
-
The importance of IoT security: A video guide
By: Palo Alto Networks
Type: Video
The advent of IoT has completely changed the nature of the modern network, and along with it, the nature of modern cybersecurity. Watch this video, in which Palo Alto looks at the importance of IoT security, and present their IoT security offering, which aims to empower your existing security.
-
Train Your Security Personnel and Enhance Security
By: SimSpace
Type: Product Overview
According to a recent study, 80% of respondents feel their organization is unprepared to handle a severe cyberattack that happens in production. The SimSpace platform provides a suite of cyber drills designed to evaluate and enhance the capabilities of cybersecurity personnel, teams, and defenses across various scenarios. Read on to learn more.
-
Futurum Research: The Future of Cloud is in the Network
By: Cisco
Type: Analyst Report
In this analyst report, learn about the 7 pillars of cloud networking and how Cisco can power your cloud-networking journey.
-
ERP buyer’s guide: Find the right solution for your business
By: Be-Terna
Type: White Paper
This ERP buyer’s guide is designed to give you the insights needed to make an informed choice on a solution that suits you best. Read the white paper now to learn how viewing ERP selection as a strategic partnership opens doors to enhanced productivity, sustained growth, and a lasting competitive advantage.
-
CW ASEAN – September 2018: Time to clear DevOps hurdles
By: TechTarget ComputerWeekly.com
Type: Ezine
ASEAN organizations are generally aware of the benefits of DevOps, but lesser known are the pathways to success. What would an organization that has successfully implemented DevOps look like?
-
Why organizations struggle to manage contractor access
By: Island
Type: White Paper
The tools organizations offer to contractors can be overly complex, expensive, and ultimately not suited to the task of effective contractor access oversight. In this editorial brief, take a closer learn how approaching these problems at the
-
How Decathlon implemented scalable security with Trend Micro
By: Trend Micro
Type: Case Study
Decathlon faced an uphill battle when it came to implementing the security side of their company-wide digital expansion. Through an implementation of Trend Micro’s suite of security products, Decathlon is able to aggressively pursue its digital vision with confidence. Read on to learn the full story.
-
MicroScope: Steering IT in the right direction
By: MicroScope
Type: Ezine
An issue looking at the timing of the ideal sales pitch and just what's happening with IoT and the channel.
-
Ask the experts: Discover how to handle external security auditors
By: Dell Software
Type: eGuide
A survey conducted at RSA Conference 2015 found that only about 68% of IT pros are honest with security auditors about the occurrence of incidents—leaving 32% in a decidedly gray area of ethics. Make the most of the audit process by learning 3 issues to consider when employing external security auditors.