Reduce Insider Threats Risk Through End User Empowerment
By: McAfee, Inc. View more from McAfee, Inc. >>
Download this next:
7 risk mitigation strategies to protect business operations
By: TechTarget ComputerWeekly.com
Type: Infographic
Without risks to manage and threats to mitigate, life in business would be a lot easier. Internal risks, external risks and threats can disrupt or destroy the four critical elements that most enterprises need to operate: people, processes, technology and facilities. Each of the four elements can have vulnerabilities.
As part of an enterprise risk management program, risk mitigation strategies must not only identify risks and threats, such as organizational risks, but also stress the importance of identifying vulnerabilities that could open the door to risk events. In this infographic, we put together the seven most widely used risk mitigation strategies to help business keep their data safe.
These are also closely related to: "Reduce Insider Threats Risk Through End User Empowerment"
-
Understand the difference between risk ratings and quantification
By: Safe Security
Type: White Paper
This paper distinguishes between cybersecurity risk ratings and risk quantification. Ratings offer a score based on security indicators but don't measure the likelihood and financial impact of cyber events. Risk quantification, however, provides a detailed financial assessment of cyber risks, aiding strategic decisions.
The text notes the limitations of risk ratings as part of a broader cyber risk management strategy. It emphasizes that risk quantification translates cyber threats into financial terms, aligning with business goals.
For insights on using risk quantification to enhance third-party risk management, consult the full paper.
-
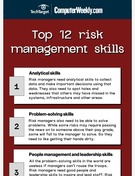
Infographic: Top 12 risk management skills
By: TechTarget ComputerWeekly.com
Type: Infographic
Risk management is a must for anyone who aspires to be a leader or manager. There is risk to be addressed at all business levels, and if a leader is unable to manage risk, their upward mobility will disappear.
Being a capable risk manager requires awareness and knowledge to uncover potential risks and present them to people best suited to solve the problem. A risk manager doesn't necessarily have to make the fix -- they just need to bring it to the person who can.
Find more content like what you just read:
-
Insuring the uninsurable: Is cyber insurance worth its salt?
By: TechTarget ComputerWeekly.com
Type: Research Content
This article in our Royal Holloway Information Security Thesis series discusses the risks and benefits of cyber insurance and outlines steps businesses can take to make better informed risk mitigation decisions.
-
How to build a risk-informed, resilient business
By: ServiceNow and TechM
Type: eGuide
Discover how to build a risk-informed, resilient business that can adapt to change and uncertainty. This e-guide explores the risks businesses face and how an effective management solution can help you seize hidden opportunities. Read the full e-guide to learn more.
-
Traditional vs. enterprise risk management: How do they differ?
By: TechTarget ComputerWeekly.com
Type: eGuide
Businesses understand they cannot exist in a risk-free environment. How to manage the risks they face depends on many variables, including the industry the business is in and its size. In this e-guide, we compare traditional risk management and enterprise risk management and outline the important differences between the two.
-
A CISO's guide to reducing risk and complexity across IT
By: Cloudflare
Type: White Paper
As cybersecurity risks expand, CISOs need a unified approach to evaluate, exchange, and enforce risk posture across users, apps, and data. Learn how to simplify risk management and optimize security investments in this e-book.
-
The state of OT risk management
By: Claroty
Type: Webcast
While all cyber risk plays an important role in your organization’s security posture, operational technology (OT) risk is specifically challenging due to its many levels of complexity. In this webcast, Claroty’s Gary Kneeland explores the state of OT cyber risk, and how you can monitor, measure, and manage your OT risk. Watch now to learn more.
-
How Dignity Used Risk Cloud® to Adapt to an Evolving Regulatory Environment
By: LogicGate
Type: Case Study
When new regulatory requirements were imposed in the U.K., the Dignity team had a significant challenge on their hands: They had to launch an entire risk and compliance program from scratch. Find out how Risk Cloud made the process easy
-
Building the Business Case for Quantifying Cyber Risk
By: LogicGate
Type: eBook
It's the cybersecurity question every executive and board member wants — and needs — to have answered: How much will it cost if a cybersecurity risk materializes and causes a breach? Provide the answer with confidence by tying cyber threats to business impact using cyber risk quantification. Read on to learn more.
-
4 steps to manage risk and resilience in real time
By: ServiceNow and Navisite
Type: eGuide
Learn how to manage risk and build resilience across your enterprise in real-time. Discover a 4-step roadmap to proactively manage technology and cyber risks, effectively report on enterprise-wide risk, maintain business continuity, and mitigate third-party and supplier risks.
-
Manage and Mitigate Enterprisewide Risk with ServiceNow Partners
By: ServiceNow
Type: Case Study
Discover how ServiceNow and its partners help enterprises manage and mitigate risk across the organization. Read these customer stories to see how they achieved quantifiable results like $2.6M in annual savings and 70% productivity gains. Read the full case study to learn more.
-
Automate cyber risk management with an AI-powered platform
By: Safe Security
Type: Product Overview
The SAFE One Platform is an AI-powered, unified solution for managing first-party and third-party cyber risks. It provides real-time visibility, enables effective board reporting, justifies security budgets, and accelerates risk decisions. Read the full datasheet to learn how this platform can empower your cybersecurity efforts.
-
Horizon Media: Spinning Up a Cyber Risk Program from Square One
By: LogicGate
Type: Case Study
As a company grows, so does its responsibility for keeping its customers’ data and assets secure. But Horizon lacked a formal cyber risk management program, which made it hard to assure their clients that they were doing all they could to keep their information safe. So, they turned to LogicGate Risk Cloud.
-
Insider Threat Detection: Guide to Prevention & Mitigation
By: Babel Street
Type: eBook
Insider threats pose a growing risk, with classified data leaking online for months before detection. Learn how AI-powered monitoring of public and commercial data can help the DoD prevent, detect, and mitigate these threats. Read the full eBook.
-
12 top enterprise risk management trends in 2023
By: TechTarget ComputerWeekly.com
Type: eGuide
Enterprise risk management has taken center stage as organizations grapple with the lingering effects of the COVID-19 pandemic, the threat of a recession and the rapid pace of change. Here are 12 security and risk management trends that are reshaping the risk landscape and influencing business continuity planning.
-
LogicGate Risk Cloud®: A Next-Generation GRC Management Platform
By: LogicGate
Type: Analyst Report
Today’s enterprises need modern governance, risk management, and compliance (GRC) software that is adaptive, integrated, and intuitive enough to meet these challenges head-on. For GRC 20/20’s Michael Rasmussen, LogicGate Risk Cloud is a top contender among those solutions.
-
Human risk & cybersecurity: What 1,000 security pros think
By: SoSafe
Type: Research Content
Cyber incidents exist as the number one business risk to organizations, according to the Allianz Risk Barometer 2023. With many bad actors leveraging social engineering techniques, organizations are pressed to understand, and defend against, the threat of human risk. For guidance, dig into this 78-page research report.
-
5 steps to mitigate cyber risk with identity security
By: SailPoint Technologies
Type: White Paper
Using identity security to mitigate cyber and corporate risk should be top-of-mind for all cybersecurity and IT risk management practitioners, and it’s not as expensive or time consuming as you might think. This white paper explores 5 key steps you can use identity security to combat the rise in risk. Download the white paper now to learn more.
-
Tackling your shadow IT risks: What you need to know
By: Auvik Networks, Inc.
Type: White Paper
Shadow IT threatens data security and compliance. In this white paper, discover examples like unapproved comms tools or personal devices, and learn how to tackle shadow IT risks and solutions.
-
Top 10 ways to anticipate, eliminate, and defeat cyberthreats like a boss
By: ServiceNow
Type: eBook
With 90% of organisations saying digital transformation introduces new risks, what if you could enable agility in technology innovation safely and confidently? Discover how easy it is to drastically improve your risk and security hygiene in this guide.
-
How to identify and manage major risks to your accounting firm
By: Intuit
Type: eBook
Building your own accounting and bookkeeping practice is rewarding when you grow and add clients. While it’s normal to maintain a strong focus on continued growth, it’s also vital to pay attention to the potential risks you may face to ensure your business keeps growing. Read on to learn how to identify and manage those risks for your firm.
-
Gain visibility on change risk to eliminate production failures
By: Digital.ai
Type: Product Overview
Predict and mitigate change failure risks in your application environment. Learn how Digital.ai Intelligence - Change Risk Prediction can help you make data-driven decisions, accelerate agility, and reduce costs associated with production incidents. Read the full product brief.
-
How great is your risk of ransomware? An assessment
By: Bitdefender
Type: eBook
Ransomware has become a booming business, complete with its own ecosystem of suppliers, specializations, and affiliate programs. Similarly, detecting and stopping a ransomware attack requires a coordinated effort — one that is risk-informed. In this eBook, learn how to evaluate your organization’s risk in the face of rising ransomware threats.
-
Embrace change management with AI
By: Digital.ai
Type: Video
The circumstances of the modern business world force today’s organizations to embrace constant change. This video introduces Digital.ai’s Change Risk Prediction (CRP) product, which uses predictive AI to help organizations account for and deal with risk as they manage change. Watch the brief video now to learn more about CRP.
-
Safety certification: Have you planned for these cost and schedule risks?
By: Wind River
Type: Webcast
This webinar examines the factors that influence a certifiable solution program schedule and details what you can do to mitigate common risks to achieve an on-time and on-budget development effort.
-
World Economic Forum Global Risks Report 2018
By: TechTarget ComputerWeekly.com
Type: Research Content
The World Economic Forum Global Risks Report 2018 identifies the top geopolitical risks facing the world in 2018. Environmental risks dominate, but cyber attacks, the risks of artificial intelligence, and the possibility of the internet defragmenting are high on the agenda.
-
A more streamlined approach to risk management
By: Claroty
Type: Product Demo
Risk is the foundation of all cybersecurity, and an effective risk management system is an essential component of your overall security infrastructure. In this video, experts from Claroty explore how Claroty xDome empowers industrial cybersecurity teams to quantify and assess organizational risk.
-
Royal Holloway: Lessons on catastrophe - differences and similarities between cyber and other forms of risk
By: TechTarget ComputerWeekly.com
Type: Resource
Cyber insurance is still in its infancy but has shown significant growth, with evidence for further expansion. However, a lack of past information and some idiosyncrasies make pricing difficult, as well as potentially amplifying risk exposure. This article summarises findings from a practical model that could be used in lieu of actuarial data.
-
Blueprint to Transform Third-Party Risk Management
By: Safe Security
Type: White Paper
Discover a 5-step blueprint to transform your third-party risk management (TPRM) program. Learn how to focus on critical controls, partner with vendors, manage risk impact, prioritize by risk, and optimize costs. Download this white paper to improve your TPRM strategy.
-
A Computer Weekly buyer's guide to compliance, risk and governance
By: TechTarget ComputerWeekly.com
Type: eGuide
Managing data compliance and security has emerged as an integral business consideration. In this 15-page buyer's guide, Computer Weekly looks at the rise of integrated risk management, security risks in the age of digitisation and how to manage an integrated approach
-
Managing M&A Risk
By: Tanium
Type: White Paper
To optimally manage cyber risk in the mergers and acquisitions process, acquiring organizations need a rapid, accurate way to map all the endpoint assets in a target company. Read about how this is done in Managing M&A Risk: How Endpoint Visibility Can Deliver Critical Advantages.
-
Navigating risk adjustment challenges for healthcare into 2024
By: ZeOmega
Type: eBook
Without risk adjustment, Medicare and Medicaid would be unable to properly provide for millions of Americans. In this comprehensive 25-page e-book, explore an analysis and forecast by ZeOmega’s experts in risk adjustment solutions,
-
Risk management is the beating heart of your cyber strategy
By: TechTarget ComputerWeekly.com
Type: eBook
In this E-Guide we will explore four separate aspects of this wide-ranging topic area, beginning with a look ahead at some of the most impactful and significant data privacy trends likely to affect your risk and compliance strategy during 2022.
-
Secure remote access: More vital than ever thanks to Covid-19
By: TechTarget ComputerWeekly.com
Type: eGuide
We explore some of the minutiae of securing the remote workforce. First, infosec consultant Kevin Beaver, picks over some remote access security risks that have arisen during the pandemic. Then we explore the findings of a recent supplier report, which detailed how remote working burn-out is becoming a factor in increasing security risk.
-
Eliminate Shadow IT threats in your organization: A practical guide
By: Auvik Networks, Inc.
Type: White Paper
Unapproved tools put organizations at risk. Learn how to govern, identify, protect, detect, respond, and recover from shadow IT. Read this white paper for a comprehensive plan to shed light on the shadows – also inside, find a self-assessment quiz that helps you determine your risk factor.
-
How to prioritize key risks and improve decision making
By: Trend Micro
Type: Product Overview
This product overview delves into Trend Micro's Risk Insights, a tool that reveals and ranks risks across identities, devices, and apps. It utilizes threat intelligence and health checks to bolster a zero-trust approach. Download now to discover how Risk Insights can help strengthen your organization’s security strategy.
-
Tanium for Cyber Insurance
By: Tanium
Type: Product Overview
Managing and protecting the thousands of devices that are connected to your network has never been more challenging. Cyber insurance is a key tool to mitigate the associated risks. Explore 10 steps for assessing cyber risk for cyber insurance when you download this guide.
-
Top 10 CI/CD security risks you can't ignore
By: Palo Alto Networks
Type: eBook
Pipelines open new attack surfaces if not secured properly. In this 42-page eBook, learn key strategies to lock down your CI/CD environments and processes to avoid data breaches, compromised infrastructure, and failed audits.
-
2023 research paper: How to secure OT environments
By: Palo Alto Networks
Type: Research Content
Though they present great opportunity, Industrial Internet of Things (IIoT) initiatives present great security risk as well as financial risk, because of the costly nature of shutting down operations. So, how can you secure your business’s OT environment and mitigate such risks? Tap into this 2023 VDC Research paper for insights.
-
Advancing your risk management maturity
By: ServiceNow
Type: eBook
Maturing your risk management programs is vital for meeting enterprise-wide objectives. Get insights on how you can raise the maturity level of enterprise risk management. You’ll discover how your teams can make decisions that lead to greater outcomes, by connecting business and IT with a common language on a single platform.
-
Eliminate your API vulnerabilities with Cequence Unified API Protection
By: Cequence
Type: Data Sheet
Today’s security teams simply lack the visibility and defense capabilities they need to protect the ever-growing risk from APIs and other application connections. Check out this data sheet to see how the Cequence Unified API Protection solution can reinforce the vulnerabilities that may undermine your organization.
-
CW ANZ, July 2020: Expert Advice on Security
By: TechTarget ComputerWeekly.com
Type: Ezine
In this handbook, Computer Weekly looks at how organisations in Australia and New Zealand can better protect themselves against evolving cyber threats.
-
How to make the most of your APIs while minimizing risk
By: Software AG
Type: White Paper
APIs can fuel growth and innovation, but also pose security risks when they are not managed properly. This white paper delves into the challenges of API proliferation, such as fragility, strategy voids, and uncontrolled growth. Read on now to find out how you can maximize the potential benefits of APIs while minimizing risks.
-
Top IT security priorities: Addressing risk management and compliance
By: Dell Software
Type: eGuide
In this expert e-guide, we explore the issues of IT risk management and compliance. You'll learn about best practices for audits, the role log reviews play in monitoring IT security, how to build authentication into access management systems, and more.
-
Explore how AI can enhance change and release management
By: Digital.ai
Type: White Paper
This whitepaper explores how AI and machine learning can enhance change and release management. Learn how predictive modeling, risk visualization, and incident prediction can make change management more agile and remove bottlenecks. Read the full whitepaper to discover the benefits of AI-powered change management.
-
Secure texting: The next great healthcare communications frontier
By: AVST
Type: eGuide
In this expert e-guide, learn why the first step to secure communications technology (like texting) is convincing leaders and clinicians to recognize the risks to health data.
-
Risk-Based Authentication
By: Cisco DUO
Type: White Paper
According to Cisco, trust should be seen as a grading of risk, where each situation is evaluated on a spectrum, and each new attempt merits a reevaluation of trust. This white paper explores how risk-based authentication (RBA) can help organizations achieve their zero-trust goal through more nuanced trust evaluation. Continue on to discover more.
-
Build a sustainable GRC program in 8 steps
By: Center for Internet Security
Type: eBook
How can you develop a sustainable governance, risk and compliance (GRC) program? Unlock insights in this 68-page e-book, which maps out how to establish a robust governance control program, conduct quantitative risk analysis, make the most of audit results, and much more.
-
Enterprise modernization via cloud adoption imperative
By: NTT & SAP
Type: Research Content
Modernizing legacy IT through cloud adoption is critical for enterprises to boost agility, efficiency and resilience. Learn how emerging technologies like AI, ML and multicloud strategies can mitigate risks and drive predictable business outcomes. Read the full research content to discover proven solutions.